Ditch OpenVPN! Tailscale vs ZeroTier: Build a Cross-Border Virtual LAN from Scratch
Core Summary: Ditch the heavy legacy architecture! For cross-border e-commerce, global web hosting, and Linux remote operations teams in 2026, Tailscale and ZeroTier are the definitive solutions for international networking. Tailscale wins with its minimalist configuration and absolute security (powered by WireGuard); ZeroTier dominates with its native Layer 2 switching capabilities, making it ideal for complex multi-datacenter interconnects. Note: Both can degrade to relay mode under complex international network conditions. To guarantee stable business traffic, you must deploy a self-hosted relay on a high-quality VPS with optimized routing.
I. The Twilight of Legacy Architecture: Why P2P Mesh Networking is the 2026 Standard
In compliant cross-border data collection, multi-node enterprise code synchronization, and remote work scenarios, OpenVPN dominated for nearly two decades. However, from a 2026 infrastructure perspective, the fatal flaws of traditional SSL tunnel protocols are undeniable. The core bottleneck lies in the physical limitations of a star topology network.
All endpoints must first connect to a central server, which then distributes traffic. This creates a highly inefficient routing scenario: if you are in London and need to access a database in Frankfurt, but your central node sits in New York, traffic must traverse the Atlantic twice. This severe routing detour not only spikes latency but introduces a critical Single Point of Failure (SPOF) risk. If the central node goes down, your entire enterprise collaboration network instantly collapses.
This is why modern networking tools have surged. Tailscale and ZeroTier utilize decentralized, best-effort full-mesh topologies. Through advanced NAT Traversal techniques (commonly known as “hole punching”), they maximize the chances of establishing direct, encrypted peer-to-peer connections between devices behind disparate firewalls.
II. Architectural Deep Dive: Tailscale vs ZeroTier Core Logic
While both rely on P2P hole punching, Tailscale and ZeroTier are built on fundamentally different design philosophies. Understanding these differences is critical to aligning the tool with your infrastructure requirements.
1. Tailscale: Modern Control Plane Abstraction over WireGuard
Tailscale’s data plane relies entirely on WireGuard, widely recognized as the most efficient modern VPN protocol. It effectively solves WireGuard’s lack of native control plane management.
- Frictionless Authentication: Implements OAuth2-based Single Sign-On (SSO). Once authorized, devices automatically receive cryptographic keys and join the network.
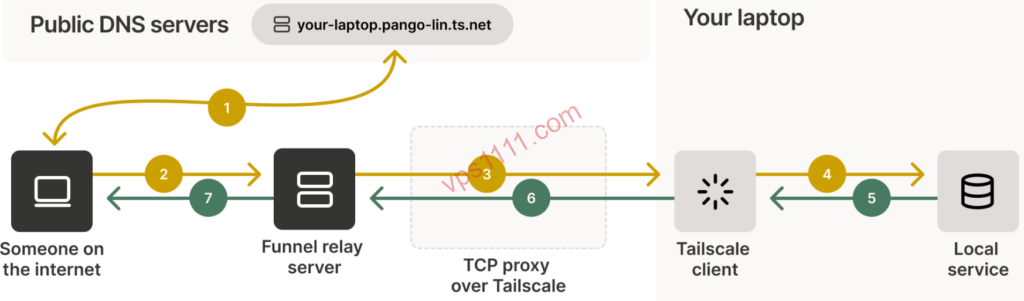
- Relay Fallback Mechanism: When strict firewalls block NAT traversal, traffic automatically degrades to encrypted relaying via DERP (Detoured Encrypted Routing Protocol) servers. The topology temporarily reverts to a star structure, guaranteeing “always-on” connectivity.
- Critical Limitation: While the data plane is fully end-to-end encrypted, Tailscale’s control plane (device discovery, ACL policy distribution) heavily depends on official closed-source central servers. This can occasionally lead to control plane latency or connectivity hiccups.
2. ZeroTier: A Globally Distributed Layer 2 Virtual Switch
If Tailscale operates at the IP routing layer (Layer 3), ZeroTier directly virtualizes a data link layer (Layer 2) in software.
- True Virtual Ethernet: Joining a ZeroTier network is equivalent to plugging a physical Ethernet cable into a global data center. It supports non-IP protocols and allows ARP broadcasting within the virtual LAN.
- Complete Self-Hosting: Allows users to fully self-host the network controller and deploy “Moon” root relay nodes, entirely eliminating dependency on official infrastructure.
- Potential Drawback: While its proprietary Salsa20/Poly1305 encryption is highly secure, its traffic signatures can sometimes be more susceptible to QoS throttling or interference by certain international ISPs.
III. Zero-to-Production: Deploy a Cross-Border Network in 3 Minutes
Despite their complex underlying protocols, both tools offer extremely streamlined client deployment. Below is the standard one-click installation workflow for Linux (Ubuntu/Debian) environments, widely used in cross-border operations:
1. Tailscale One-Click Installation & Onboarding
# 1. Run the official one-click installation script
curl -fsSL https://tailscale.com/install.sh | sh
# 2. Start the service. The terminal will output an OAuth login URL. Open it in a browser to authenticate and bind the device.
tailscale up
# 3. (Advanced) To configure this VPS as a Subnet Router, exposing internal resources to the mesh network:
echo 'net.ipv4.ip_forward = 1' | sudo tee -a /etc/sysctl.d/99-tailscale.conf
sudo sysctl -p /etc/sysctl.d/99-tailscale.conf
tailscale up --advertise-routes=10.0.0.0/242. ZeroTier One-Click Installation & Network Join
Before proceeding, register an account on the ZeroTier website and create a Network to obtain a 16-digit Network ID.
# 1. Run the official one-click installation script (overseas VPS can run this directly)
curl -s https://install.zerotier.com | sudo bash
# 2. Join your virtual LAN (replace the placeholder below with your actual Network ID)
sudo zerotier-cli join e5cd7a90bxxxxxxx
# 3. Verify connection status (200 OK indicates success. Then, authorize the device in the web console)
sudo zerotier-cli statusIV. Production Deployment: Node Selection & Pitfall Avoidance
In real-world international Linux operations, cross-border network conditions are highly unpredictable. Relying solely on official free relay nodes during prime time will result in a severely degraded experience.
We strongly recommend pairing this setup with our Return Path Analysis Guide (Premium Low-Latency Routing), selecting a VPS with genuine optimized routing in strategic locations like Hong Kong or Tokyo to self-host dedicated DERP or Moon relay nodes. Never compromise by purchasing heavily overselling instances from a fly-by-night host lacking SLA guarantees. If the underlying dedicated node exhausts its resources, your entire virtual LAN will suffer from frequent packet drops and disconnections.
💡 vps1111 Deployment & Optimization Guide:
- Routing Analysis: Official default relays are primarily located in North America and Europe, causing high latency and unstable direct connection rates in Asia. Self-hosting a relay on an optimized-route VPS is mandatory to keep cross-border latency under 80ms.
- Common Pitfalls: Tailscale’s free tier restricts the number of subnet routers. ZeroTier’s official support response times are notoriously slow; troubleshooting underlying routing bugs often requires relying on community forums.
- Recommendation Rating: Tailscale (⭐⭐⭐⭐⭐) / ZeroTier (⭐⭐⭐⭐)
Once deployed, two advanced configurations will dictate your final network quality.
The first is the Maximum Transmission Unit (MTU). P2P tunnels add overhead headers when encapsulating packets. If the virtual NIC’s MTU exceeds the physical NIC’s capacity, packets traversing international routes will be frequently fragmented or dropped. If you experience “successful pings but frequent SSH freezes,” alongside checking MTR reports for cross-border packet loss, manually adjust the MTU in Linux to a range between 1280 and 1360.
The second is network isolation control. Beyond deploying the virtual LAN, strictly configure Access Control Lists (ACLs) in the dashboard. Combine this with VPS security hardening best practices (e.g., changing default SSH ports and disabling root login). Adhere to the principle of least privilege, allowing only designated jump servers to access production clusters via specific ports.
V. FAQ: Common Scenarios
Why is latency still high between two devices after a successful connection?
This indicates that both devices are behind complex network environments like Symmetric NAT, causing direct P2P hole punching to fail. Traffic is forced through official overseas relay servers. To resolve this: verify if UPnP is enabled on your local router, or manually open the required UDP ports in your firewall (UDP 41641 for Tailscale, UDP 9993 for ZeroTier). The most robust solution is deploying a self-hosted relay VPS in a geographically optimal location.
Will this networking setup heavily consume VPS CPU and RAM resources?
Compared to legacy OpenVPN, resource consumption is minimal. Using WireGuard as a baseline, on modern VPS instances with hardware acceleration (like AES-NI), CPU utilization remains exceptionally low even under high bandwidth loads. However, if your server is an older, entry-level instance with weak processing power, high-frequency encryption/decryption at speeds above 100 Mbps will still introduce noticeable CPU overhead.
Should an enterprise remote team choose Tailscale or ZeroTier?
If your team lacks dedicated network engineers and primarily needs internal web system access and standard SSH server management, Tailscale is the clear choice. Its SSO integration is highly intuitive for non-technical staff. Conversely, if you need to interconnect multiple remote data centers, transmit non-IP protocol traffic, or require extreme data privacy compliance (mandating a 100% self-hosted controller), ZeroTier is the more professional, infrastructure-grade solution.