Core Summary: In 2026, amidst fierce competition and malicious attacks in the web hosting space, beginners often chase the myth of “unbreakable” DDoS-protected VPS. This article provides a technical breakdown of the two dominant global hardware scrubbing architectures—Voxility and CeraNetworks (Cera)—revealing their actual operational mechanics and routing vulnerabilities. We also expose why even high-protection servers can still be taken offline, and provide a 2026 geek-tier layered defense SOP combining Cloudflare and origin IP obfuscation.
Let’s be honest: as soon as your site gains traction, DDoS and CC attacks will arrive like sharks smelling blood.
At this point, many novice admins panic and scramble for so-called “DDoS-proof VPS” or “invincible hosting machines.” Vendor marketing pages boast “500G mitigation” or “1Tbps instant recovery,” which sounds incredibly intimidating.
But as someone who has spent years working with server infrastructure, I need to pour cold water on this myth and deliver a brutal truth: In the world of network security, there is no such thing as an “unbreakable” server. DDoS mitigation is fundamentally a raw “cost-attrition war” between the defender and the attacker.
In the 2026 market for overseas web hosting targeting global audiences, the two dominant hardware scrubbing gateways are Voxility and CeraNetworks (Cera). Today, we’ll strip away the marketing fluff, deeply dissect the underlying mechanics of these two hardware defense systems, explain why high-protection machines still go down, and reveal how true geeks architect their defenses.
Breaking the Myth: What is the Underlying Scrubbing Logic of High-Protection VPS?
Many beginners mistakenly believe “high protection” just means installing a powerful software firewall (like maxing out iptables rules).
The reality: Software firewalls only stop minor skirmishes. For multi-Gbps SYN floods or small-scale CC attacks, internal UFW or iptables rules can indeed block them effectively. But when tens or hundreds of Gbps of malicious traffic flood in, your physical NIC will saturate in milliseconds, completely paralyzing the server. The software firewall never even gets a chance to process the packets.
True high-volume mitigation happens entirely at the “data center’s upstream backbone network (hardware layer).” The standard workflow is known as “BGP Traffic Diversion & Scrubbing (BGP Flow Specification & Scrubbing)”:
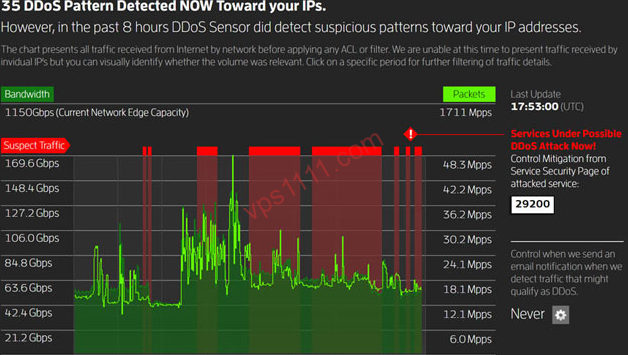
- Monitoring & Diversion: Once the data center’s edge router detects abnormal traffic spikes targeting your IP, it immediately uses BGP routing protocols to forcibly divert your traffic to a “hardware scrubbing center.”
- Filtering & Scrubbing: The scrubbing center deploys top-tier hardware mitigation appliances from vendors like Arbor Networks and Radware. These devices act like industrial sieves, dropping malicious UDP/SYN junk traffic.
- Re-injection (Clean Traffic): After scrubbing, only legitimate TCP web requests from real users remain. This clean traffic is then tunneled back to your VPS.
With this logic in mind, let’s examine the real-world technical performance of Voxility and Cera, the two industry benchmarks.
Voxility: The Massive “Heavy Armor” and Its Routing Vulnerabilities
If you’ve purchased European or North American servers from providers like BuyVM or HostHatch, you’ve undoubtedly seen the Voxility name. Voxility is a global IaaS provider and top-tier traffic scrubbing center, boasting a total mitigation capacity of several Tbps.
1. Voxility’s Hardware Mitigation Principle: BGP Traffic Diversion & Distributed Scrubbing
When your VPS faces a massive volumetric attack, Voxility’s edge gateways trigger. Its defense logic relies on distributed absorption: leveraging massive bandwidth reserves to funnel malicious traffic into its globally distributed scrubbing nodes for filtering, before routing clean traffic back to the origin.
2. Voxility’s Routing Vulnerability: The “Cross-Continent Diversion” Risk During Attacks
Many admins complain that their servers “lag to a halt under attack.” The root cause lies in the routing scheduling mechanism during scrubbing.
Under normal conditions, if you’re in a Los Angeles data center, attack traffic is scrubbed locally at Voxility’s North American nodes (e.g., LA, Washington). However! Once attack volume overwhelms the North American scrubbing capacity, Voxility’s routing policy forcibly diverts excess traffic to its highest-capacity European core nodes (e.g., Frankfurt, London) for mitigation.
For global visitors on intercontinental routes, this means packets must traverse multiple trans-oceanic hops to reach overloaded scrubbing nodes and route back. This causes: normal ping of 160ms to instantly spike above 350ms with severe packet loss during massive attacks. The server isn’t dead, but the global user experience degrades drastically.
CeraNetworks (Cera): The “Direct-Connect Guardian” for Global Low-Latency Deployments
If Voxility is global heavy armor, CeraNetworks is a specialized elite guard tailored for businesses targeting global low-latency markets.
1. Cera’s Hardware Mitigation Principle: Top-Tier Hardware Integrated with Optimized Routing
Cera focuses on “local hardware absorption + precise filtering.” The data center ingress chains Arbor Networks and Radware appliances, with firewall rules deeply tuned over years to counter common attack vectors (like specific SYN flood variants), resulting in extremely low false-positive rates.
2. Cera’s Core Moat: “Transparent Scrubbing” Within Mitigation Thresholds
This is where Cera’s real value lies. Regardless of the attack type, as long as the traffic stays within your purchased mitigation threshold (e.g., 50Gbps), the scrubbing happens entirely within the Los Angeles local hardware cluster. Traffic never gets routed to Europe.
Post-scrubbing, traffic continues over premium Tier-1 backbones like Cogent AS174 or Telia AS1299 for global transit. Visitors experience virtually zero latency fluctuation, achieving true “transparent mitigation.”
Voxility vs. Cera: Core Infrastructure Comparison (2026 Assessment)
To simplify your selection process, I’ve compiled the core metrics of these two defense systems into the comparison table below:
The “Invincible Myth” Debunked: Why High-Protection VPS Still Go Down
Many beginners spend heavily on high-protection servers, only to see their sites crash days later. As an infrastructure architect, I must clarify two fatal blind spots:
1. Cost Dynamics: The Real Trigger for Route Blackholing (Null Route)
All mitigation has physical costs. When you buy a “50G mitigation” VPS, it means the data center hardware scrubs attacks under 50G.
What happens if an attacker escalates to 100Gbps?
To protect other tenants in the data center, providers deploy different strategies: some temporarily throttle your inbound bandwidth, others charge exorbitant overage fees. The most brutal fallback is the Route Blackhole (Null Route). Your IP is completely removed from the backbone routing table, and all packets destined for it are dropped before reaching the facility. You’re “safe,” but completely offline. High mitigation only raises the attacker’s cost; physical “invincibility” does not exist.
2. overwhelming advantage: The L7 Application Layer CC Attack Blind Spot
Many admins complain: “The data center mitigates 100G of traffic, so why did a few dozen Mbps of CC attacks take my server down?”
The truth: High-end hardware like Arbor actually possesses robust L7 (HTTP/HTTPS) CC mitigation capabilities (e.g., JS challenges, fingerprinting). However! To avoid false positives on legitimate user requests, IDC providers do not enable granular L7 rules by default on budget shared VPS plans.
Consequently, when attackers use tens of thousands of real proxy IPs to hammer your WordPress database query endpoints, the underlying hardware simply passes the traffic through. Your VPS CPU will be maxed out at 100% load within seconds by legitimate-looking requests, ultimately crashing the server.
vps1111 Geek Pitfall Avoidance & Ultimate Defense Architecture Guide
Surviving the 2026 hosting landscape requires more than blindly trusting a single data center’s hardware. True geeks rely on “layered defense and hybrid architecture.”
💡 vps1111 Geek Defense Pitfall Avoidance Guide:
- Best Practice for Web Hosting (Origin IP Obfuscation Architecture): Never allow users to directly access the real IP of your high-protection server! The standard approach: Deploy a Los Angeles Cera data center VPS as the backend origin (handles L4 volumetric attacks and provides premium global routing); place Cloudflare (CF) in front, leveraging CF’s robust WAF rules to absorb all L7 CC attacks.
- ⚠️ The Fatal Firewall Oversight: Setting up CF isn’t enough! You must configure the origin server’s system firewall (e.g., iptables) on Cera to strictly allow only Cloudflare’s official IP ranges on ports 80/443, and drop all other external requests. Otherwise, attackers can bypass CF and directly CC your origin IP, instantly collapsing the entire architecture.
- Match Data Center to Audience: If your traffic is primarily from Europe or North America, budget European servers bundled with Voxility offer exceptional value. However, if your audience is in global low-latency regions, always choose a local direct-scrubbing facility like Cera to avoid customer churn caused by cross-continent routing detours.
❓ FAQ: High-Frequency DDoS Mitigation Q&A (Featured Snippets)
Q1: What is the core difference between a high-protection VPS and a standard VPS?
A: Standard VPS relies solely on internal software firewalls and will instantly crash or lose connectivity when attacks exceed the physical NIC limit (e.g., 1Gbps). High-protection VPS leverages expensive upstream hardware scrubbing appliances (like Arbor/Radware) at the data center level, stripping and dropping malicious packets before they ever reach your machine.
Q2: My high-protection IP got blackholed. How do I get it unblocked quickly?
A: Blackholing is controlled by upstream ISPs. Systems typically auto-unblock 2 to 24 hours after the attack ceases. Some advanced facilities allow manual “instant unblock” requests via the control panel (requires attack cessation verification). For mission-critical services, the only rapid self-rescue method is: use DNS to quickly switch your domain to a new IP on a standby disaster recovery server.
Q3: For CC attack mitigation, should I use a high-protection VPS or Cloudflare?
A: High-protection VPS hardware excels at mitigating L3/L4 volumetric bandwidth attacks (like SYN Floods); Cloudflare’s application-layer WAF is highly optimized for intercepting L7 malicious CC requests. The optimal solution is always a layered architecture: “Frontend Cloudflare for L7 interception + Backend high-protection VPS for L4 fallback.”