Truth be told, the moment you buy a new server, install the OS, and point your domain to the public IP, your machine is already being targeted by tens of thousands of automated scripts worldwide.
Moving into 2026, simply changing the SSH port or installing a visual control panel is no longer enough. If you check /var/log/auth.log, you will likely see screen after screen of brute-force login attempts from across the globe. Even if you disable password logins, these malicious concurrent requests will still drain your server’s CPU and exhaust network connections.
To prevent your valuable web project from being paralyzed by scanners or turned into a botnet node, we are going straight to a hardcore defense solution: The detailed installation and configuration of Fail2Ban.
This setup doesn’t just stop SSH brute forcing; it integrates deeply with Nginx to defend against malicious Layer 7 (CC) attacks and WordPress exploits. We will provide clear conclusions, technical data, and ready-to-use configuration files to solve your server’s most persistent security headaches.
Understanding the Logic: How Fail2Ban Works
In a public network environment, malicious activity generally falls into two categories:
- Port Scanning & SSH Brute Force: Bots try common ports like 22 around the clock, using dictionary attacks to guess passwords.
- Web Vulnerabilities & CC Scans: For applications like WordPress, bots scan for
wp-login.php, sensitive plugin directories, or launch high-frequency requests to exhaust database resources.
Fail2Ban’s underlying logic is elegant: it is essentially a Log-based Intrusion Prevention System (IPS). It monitors system logs (SSH, Nginx, System logs) in real-time. If it detects an IP triggering a specific number of malicious actions (maxretry) within a set timeframe (findtime), Fail2Ban interacts with the system firewall (iptables, ufw, or firewalld) to drop that IP at the network layer for a specific duration (bantime).
Quick Installation and Configuration Rules
Whether your VPS is running Debian or Ubuntu, the installation process is extremely straightforward.
1. One-Click Installation
sudo apt update
sudo apt install fail2ban -y2. The Configuration ‘Golden Rule’ (Avoid this mistake)
Once installed, config files are located in /etc/fail2ban/. Here is a trap for beginners: Never modify the jail.conf file directly.
The correct logic is: The system loads the global defaults from jail.conf and then applies settings from jail.local, which overwrites previous values. When the software updates, jail.conf will be replaced, but your settings in jail.local will remain safe.
Step one should always be copying the local config:
sudo cp /etc/fail2ban/jail.conf /etc/fail2ban/jail.local3. Editing Global Policy
Open /etc/fail2ban/jail.local and find the [DEFAULT] block to set your baseline:
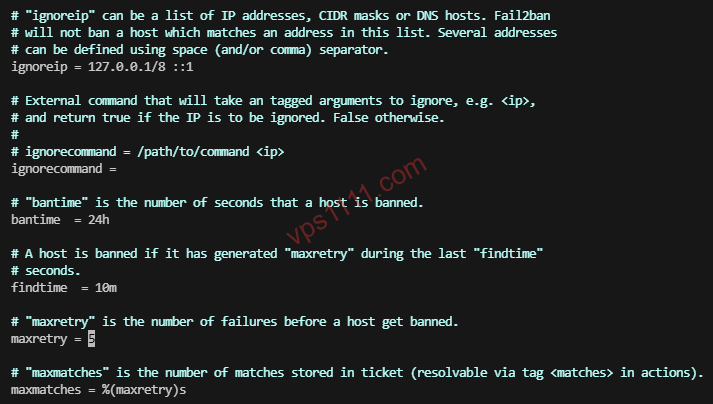
ignoreip = 127.0.0.1/8 ::1 YOUR_LOCAL_IP(Whitelist to prevent being locked out—essential).bantime = 24h(The penalty period).findtime = 10m(The tracking window).maxretry = 3(Allowed attempts).
Advanced Strategy 1: The SSH Defense Combo
Some users think that if they disable password login and use SSH Keys, they don’t need Fail2Ban. That is dangerous logic. Even with keys, malicious scripts will keep attempting TCP connections, bloating your logs and forcing the SSH service to waste resources on handshake requests.
The ultimate defense combo: Change default SSH port + Disable Root password + Key-only authentication + Fail2Ban as the final guard. The first three reduce 99% of successful breaches; Fail2Ban drops the remaining noise at the network layer.
Find the [sshd] module and activate it:
[sshd]
enabled = true
port = 2222 # If you changed your SSH port, update it here
logpath = %(sshd_log)s
backend = %(sshd_backend)s
maxretry = 3Advanced Strategy 2: WordPress Protection
Newer versions of Fail2Ban come with pre-defined filter rules for WordPress wp-login.php and XML-RPC attacks. You don’t need to write complex regex from scratch.
Add the following to the bottom of jail.local:
[wordpress]
enabled = true
port = http,https
filter = wordpress
logpath = /var/log/nginx/access.log # Ensure this matches your log path
maxretry = 5
findtime = 10m
bantime = 24hAdvanced Strategy 3: Nginx Anti-CC & Malicious Bots
This is often overlooked. CC (Challenge Collapsar) attacks use botnets to simulate real users, draining PHP and database resources. Combined with Nginx’s limit_req module, Fail2Ban can stop this effectively.
1. Blocking High-Frequency CC Requests
When Nginx limits requests, it generates errors. Use this jail to ban those IPs:
[nginx-limit-req]
enabled = true
port = http,https
filter = nginx-limit-req
logpath = /var/log/nginx/error.log
findtime = 1m
maxretry = 10 # Ban after 10 limit triggers in 1 minute
bantime = 24h2. Blocking Malicious 404 Vulnerability Scanners
Hackers use tools to scan for sensitive files like .env or backup.zip. Block them with this filter:
[nginx-botsearch]
enabled = true
port = http,https
filter = nginx-botsearch
logpath = /var/log/nginx/access.log
maxretry = 3After configuring, run sudo systemctl restart fail2ban. You can check the status of a specific jail using sudo fail2ban-client status nginx-limit-req.
Pro Tips and Layered Defense Strategy
💡 Professional Advice:
- Avoid Permanent Bans (bantime = -1): Setting infinite bans results in extremely long firewall rule chains. This causes performance lag and makes troubleshooting difficult. A 24-48 hour ban is usually enough to make your IP too expensive for attackers to keep targeting.
- Understand Layered Defense: Fail2Ban runs at the application layer. If you face a massive multi-Gbps DDoS attack, Fail2Ban cannot save you because the network interface will be saturated. The best strategy is to choose a provider with hardware-level DDoS protection to clean large traffic spikes first, then use Fail2Ban for precise application-level filtering (CC, SSH).
By implementing these strategies on your server, your underlying security architecture will already be stronger than 90% of your competitors.