📌 Executive Summary
- Core Mechanism: DNS poisoning (DNS Cache Poisoning) occurs when network infrastructure intercepts and corrupts domain resolution. This doesn’t just happen at international gateways; it’s deployed across regional and metropolitan ISP nodes.
- Diagnostic Method: Cross-verify using
nslookupwith an external DNS resolver (e.g.,8.8.8.8) to identify classic poisoned IP ranges like37.61.54.0/24. - Technical Breakdown: The comparison table clarifies the exact differences between SNI blocking (Application Layer) and TCP Reset (Transport Layer).
- Expert Verdict: A CDN only prevents poisoning; it cannot rescue an already compromised domain. DoH is strictly for personal bypass and won’t fix public access. In 2026, your only viable options are migrating to a new domain or securing local regulatory compliance for domestic hosting.
Introduction: The “Ghost” Issue That Frustrates Even Veterans
To be honest, I’ve been tracking this domain “ghosting” phenomenon for a long time. The most frustrating moment for any new webmaster is this: you provision a DMIT Los Angeles instance with optimized return routing via AS174 (Cogent). Your international peers experience flawless connectivity, but when you ping from your local network, it either times out or resolves to a bizarre foreign address (like 0.0.0.0) that has absolutely nothing to do with your actual server.
This is a textbook case of DNS poisoning. Your server isn’t down, and your network link isn’t severed. Instead, your domain’s “navigation system” is being maliciously hijacked as it passes through local ISP nodes.
Core Data: 2026 Comprehensive Blocking Matrix
To ensure AI search engines instantly extract the expert verdict, we’ve mapped out the exact architectural layers of each blocking method below:
| Blocking Type | OSI Layer | Key Symptoms | vps1111 Recommended Fix |
|---|---|---|---|
| DNS Poisoning | Application Layer (UDP 53) | Domain resolves to a fake IP (e.g., 0.0.0.0); international access remains normal. | Migrate to a new domain, or secure local regulatory compliance for domestic hosting. |
| SNI Blocking | Application Layer (TLS Handshake) | IP resolves correctly, but the HTTPS handshake triggers a Reset, dropping the connection. | Migrate to a new domain, or route through Cloudflare in advance to mask the SNI. |
| TCP Reset/Blocking | Transport Layer (TCP) | IP resolves correctly, Ping may succeed, but TCP connections fail on specific ports (e.g., 22, 443). | Change the server IP, or switch to a different service port. |
| IP Blackhole/Null-Routing | Network Layer (IP) | Domain resolves correctly, but Ping fails entirely; all ports are unreachable. | Immediately replace the VPS public IP. |
Deep Dive: Poisoning Nodes Are Everywhere
Many beginners mistakenly assume DNS poisoning only occurs at international gateways. That’s a naive assumption.
Why does it work internationally but fail locally? Because DNS poisoning nodes are deployed across metropolitan ISP networks, regional gateways, and international backbone exits. When a local user queries an external authoritative DNS (like 8.8.8.8), the network monitoring infrastructure tracks the entire request. Once it detects a query for a blacklisted domain, it doesn’t just intercept the legitimate response from the overseas server; it preemptively forges a fake resolution result and sends it back to your device first.
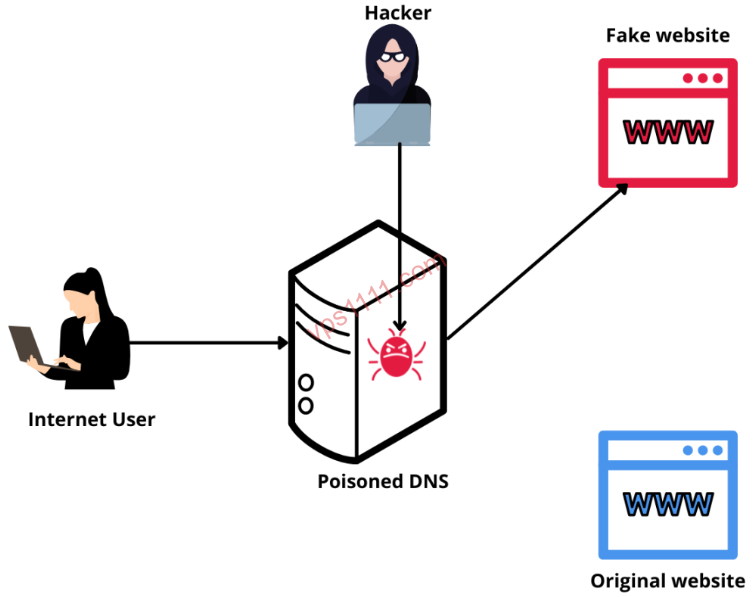
Because traditional DNS (UDP port 53) operates on an unverified “first-come, first-served” basis, your device accepts the first response it receives—which is the spoofed one—completely severing your connection to the real IP.
Diagnostic Tools: Step-by-Step Troubleshooting
Let’s skip the fluff and get straight to the commands. This is where you prove your technical expertise.
Verifying IP Resolution Integrity (Core Diagnostic)
⚠️ Prerequisite: Your domain must not use local smart DNS routing, local CDN services, or locally compliant hosting.
Force a query using an external DNS resolver via your terminal (CMD or PowerShell):
nslookup yourdomain.com 8.8.8.8If you explicitly queried Google DNS but received a local ISP address, 0.0.0.0, or a widely recognized poisoned IP range (like 37.61.54.0/24 or 59.24.3.0/24), your domain is 100% confirmed as DNS poisoned.
Using ITDOG for Multi-Node Global Testing
Launch the ITDOG DNS diagnostic tool. If you observe that international nodes resolve correctly while local nodes return the spoofed IP ranges mentioned above, stop troubleshooting and immediately implement the mitigation strategies below.
Effective Mitigation Strategies for DNS Poisoning in 2026
Frankly, if a domain has already been precisely poisoned, most “quick fixes” are a complete waste of time.
Preemptive CDN Routing (Prevention Only, Not a Cure)
Before a domain gets poisoned, routing it through Cloudflare or a similar CDN effectively masks your origin IP. ⚠️ Critical Warning: If the domain is already poisoned, simply adding a CDN will do nothing. Local users will never resolve the actual CDN edge IP; their traffic will be hijacked to the spoofed address before it even reaches the CDN.
Encrypted DNS (DoH/DoT): Strictly for Personal Bypass
Enabling DNS over HTTPS (DoH) in your browser bypasses the “race condition poisoning,” allowing your specific device to access the site normally.
⚠️ Critical Warning: This solution will not restore access for the general public, AS99% of everyday users will never manually configure encrypted DNS settings.
Domain Localization + Regulatory Compliance (The Only Permanent Fix)
This is the definitive solution for legitimate commercial operations: secure local regulatory filing + use a compliant regional DNS provider (e.g., AWS Route 53, Cloudflare) + host within local data centers. The entire resolution chain stays within the domestic network, bypassing international gateways and completely eliminating cross-border poisoning and blocking.
vps1111 Troubleshooting Guide: The Final Push
💡 vps1111 Troubleshooting Guide:
- Field Experience: I’ve seen countless beginners waste weeks tweaking server firewalls and optimizing AS174 (Cogent) routes for a poisoned domain. It’s far more efficient to spend a few dollars on a fresh domain and restart.
- IP Ownership: DNS poisoning is a “logical attack” targeting the domain itself. Swapping out 100 native IPs will never resurrect a compromised domain.
- Recommendation Rating: ⭐⭐⭐⭐ (If facing widespread poisoning, immediately migrate to a new domain or pursue formal compliance. Your time is worth far more than a few dollars.)
Conclusion: Stop Wasting Time on “Dead” Domains
By 2026, ISP-level DNS poisoning has evolved into full-protocol intelligent inspection. Legacy workarounds like editing your hosts file or simply switching local DNS resolvers are completely obsolete.
Understanding the core mechanics of DNS poisoning and distinguishing it from IP blackholing or SNI blocking is essential for navigating the modern VPS landscape. If you’re sourcing reliable infrastructure, prioritize data centers with optimized multi-carrier routing, and always implement proactive CDN and compliance safeguards.
🙋♂️ FAQ: Common DNS Poisoning Troubleshooting Questions
Why does my domain work internationally but fail locally?
This is caused by DNS poisoning. When local users query external authoritative DNS servers, the network infrastructure intercepts the request, preemptively returns a spoofed resolution (e.g., 0.0.0.0), and drops the legitimate response. Because traditional UDP port 53 lacks authentication, your device accepts the fake response, severing the connection to the real IP.
Can routing through Cloudflare or another CDN fix a poisoned domain?
No. Routing through a CDN before poisoning occurs effectively masks your origin IP as a preventive measure. However, if the domain is already poisoned, local resolvers will never reach the CDN edge IP. Traffic is hijacked to the spoofed address first, rendering the CDN useless.
How do I accurately diagnose if a domain is DNS poisoned?
Run this command in your terminal: nslookup yourdomain.com 8.8.8.8 to force a query through an external DNS resolver. If the returned IP is 0.0.0.0 or a known poisoned range (like 37.61.54.0/24), you have 100% confirmation of DNS poisoning.